Your Cart is Empty
TALK TO AN EXPERT: 1-844-945-3625
Menu
-
- Water Filter Systems
- Portable Solar Generators
- Propane Wall Heaters
- Composting Toilets
- DIY Buildings & Kits
- Canvas Tents
- Homestead & Off Grid Supplies
- Chicken Coops
- Harvest Right Freeze Dryers
- Emergency Food Kits
- Hunting Blinds
- MrCool DIY Mini Splits
- Solar Air Conditioners
- Solar Fridge & Freezers
- Camping Coolers
- Electric Coolers
- Overlanding Gear
- Two Person Cots
- Portable Sauna Tents
- Incinerating Toilets
- Dairy Equipment
- Coolers
- Faraday Defense
- EMP Shield
- Hunting Blinds
- Compost Tumblers
- Drip Irrigation Kits
- Shade Cloth
- Propane Fireplace
- Portable BBQ's
- Brands
- Chicken Coop Brands
- Composting Toilet Brands
- Solar Brands
- Food Storage Brands
- Freeze Dryer Brands
- Water Filtration Brands
- Incinerating Toilet
- Waterless Toilet Brands
- Heater Brands
- EMP Shield Brands
- Tent Brands
- Cot Brands
- Cooler Brands
- Dog Kennels
- Greenhouse & Gazebo Brands
- Portable Saunas
- DIY Shed Kits
- About Wild Oak Trail
- Resource Center
- The Ultimate Prepper & Emergency Survival Blog - Includes Free eBook
- Beginners Guide to Living off The Grid - Includes Free eBook
- Building Your Own Emergency Food Supply
- Best Survival Food to Be Prepared for Anything
- Berkey Lab Tests & Certifications
- Federal Solar Tax Credit - What You Need to Know
- BLOG
-
- 1-844-945-3625
- Login

TALK TO AN EXPERT: 1-844-945-3625
Do Police Use Faraday Bags?
by Patricia Turla 5 min read
In today's digital age, the preservation of digital evidence has become essential in law enforcement and military operations. Imagine the frustration of a law enforcement officer who loses evidence because it was tampered with remotely—an infuriating and all-too-possible scenario.
To prevent such situations, the use of Faraday bags is necessary. These bags are specially designed to block radio signals, ensuring that electronic devices stored within them remain secure and free from remote access. So, do police use Faraday bags? Absolutely, and for very good reasons.
What Are Faraday Bags?
A Faraday bag is a flexible enclosure made of multiple layers of metallic material, typically copper or aluminum, designed to block electromagnetic fields. Named after the scientist Michael Faraday, who invented the Faraday cage, these bags prevent signals such as Wi-Fi, Bluetooth, GPS, and other radio frequencies from penetrating the material. This shielding effect maintains the integrity of digital evidence in law enforcement and military operations.
Types of Faraday Bags Available
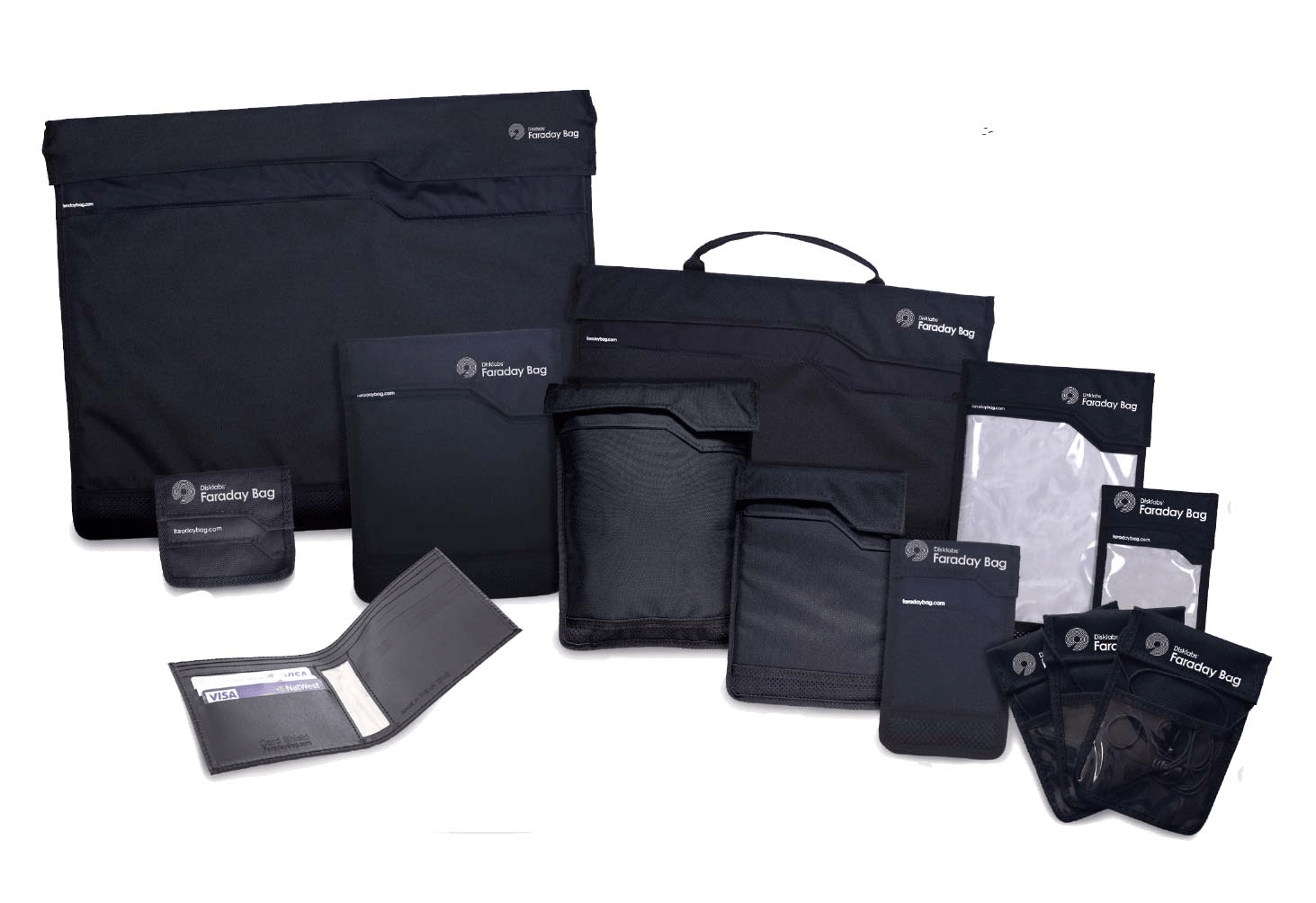
Other bags come in various shapes and sizes to accommodate different types of electronic devices, such as:
-
Phone Faraday Bag: designed to shield smartphones from radio signals, preventing tracking or remote access.
-
Tablet and Laptop Faraday Bag: Larger versions that can protect tablets and laptops, securing data on these larger devices.
-
Key Fob Faraday Bag: Small pouches specifically made to block signals from key fobs, preventing thieves from intercepting the signal to steal a vehicle.
-
Backpack Faraday Bag: These multifunctional bags not only hold your gadgets but also protect them from electromagnetic interference.
-
Evidence Collection Faraday Bag: Used by law enforcement to secure electronic evidence at crime scenes, ensuring that information remains intact for forensic analysis.
Why Police Use Faraday Bags?

Digital evidence is often as important as physical evidence in solving most cases of crimes. Law enforcement officers frequently encounter electronic devices such as phones, tablets, and computers at crime scenes. These devices can hold critical evidence, including text messages, emails, GPS data, and more. However, if left unprotected, they are also vulnerable to remote wiping or tampering.
Preserving Evidence
Police use Faraday bags to preserve the integrity of digital evidence. When a suspect's device is confiscated, there is a risk that the person could remotely access and delete data before it can be analyzed. By placing the device in a Faraday bag, officers can ensure that it is shielded from any incoming or outgoing signals, effectively freezing its state until forensic investigators can examine it.
Blocking Remote Access
Faraday bags are useful in preventing remote access to devices that contain active RFID or relevant Wi-Fi signals. Criminals sometimes use these signals to remotely connect to their devices and erase incriminating evidence. Faraday bags provide a simple yet effective solution to this problem by blocking all signals, making it impossible for anyone to tamper with the device from a distance.
Ensuring Proper Handling
Improper handling or storage of digital devices can lead to data loss or corruption. For instance, a phone might lose its charge or a computer's hard drive could be damaged if not handled carefully. Using Faraday cages or multiple layers of protection can help shield devices from damage and signal interference during transport and storage.
Legal and Ethical Considerations
There are strict legal and ethical guidelines surrounding the collection and use of digital evidence. Law enforcement authorities must ensure that they have the proper warrants and permissions before accessing a suspect's devices. Any breach of these protocols can lead to the evidence being deemed inadmissible in court.
Common Types of Digital Evidence
Digital evidence can come from a wide range of electronic devices. Some of the most common sources include:
-
Smartphone: Contains call logs, text messages, emails, photos, videos, and app data.
-
Laptop and Computer: These devices can provide access to emails, documents, browsing history, and other digital footprints that can be linked to criminal activities.
-
GPS Device: Track a suspect's movements and establish their presence at a crime scene.
-
Tablet: Similar to smartphones, tablets can store a wide array of information, including communications and app usage.
-
Key Fob: Track the vehicle movements of a suspect, providing key evidence in cases involving travel and location tracking.
Military Applications of Faraday Bag
The military also employs Faraday bags for similar reasons. In military operations, securing communication devices and protecting sensitive information from being intercepted or tampered with is paramount. Faraday bags are used to shield equipment from electronic eavesdropping and to safeguard data during transport.
-
Protecting Communication Devices:Military personnel often carry communication devices that are vital for mission success. These devices can be vulnerable to interception or jamming by adversaries. By storing them in Faraday bags, military forces can ensure that their communications remain secure and uninterrupted.
-
Securing Sensitive Data:Besides to communication devices, the military also uses Faraday bags to protect other electronic equipment and data storage devices. These bags prevent unauthorized access and ensure that sensitive information is not compromised during operations.
Faraday Bags in Crime Scene Investigations

At a crime scene, law enforcement officials must act quickly to save evidence. Faraday bags are an essential tool in this process, providing a reliable method for preserving digital devices that might contain essential information about the crime.
Securing Electronic Devices Upon Collection
Crime scenes often contain a lot of electronic device such as phones, tablets, laptops, and even key fobs. Upon collection, these devices are immediately placed into Faraday bags. The primary reason is to block any potential remote access attempts that could alter or delete data. For instance, suspects or accomplices might try to wipe a device remotely using active RFID or relevant Wi-Fi signals. By placing the device in a Faraday bag, investigators ensure it is shielded from all external signals, maintaining the integrity of the evidence.
Maintaining the Chain of Custody
The chain of custody is a critical process in criminal investigations, ensuring that evidence remains untampered from the moment it is collected to when it is presented in court. Once an electronic device is placed in a Faraday bag at the crime scene, it is transported and stored in this protected environment until it reaches the forensic lab. This uninterrupted signal blocking prevents any potential data manipulation during transit, which could compromise the investigation. Without such protection, even the slightest signal could activate, lock, or connect the device to external networks, leading to potential data loss or contamination.
Protection of Personal Device
Officers often carry phones and other electronic devices that can be vulnerable to tracking or hacking by criminals. By using Faraday bags, officers can protect their equipment from unwanted access, ensuring their safety and operational security.
Supporting Overall Security Investigative Processes
By ensuring that an electronic device cannot be tampered with remotely, a Faraday bag enhances the reliability of the evidence. In turn, it supports the investigative process by providing a clear, unaltered trail of data. From GPS data on a suspect's phone to communications on a tablet, the secure environment created by Faraday bags allows investigators to piece together accurate timelines and interactions without the risk of external interference.
Conclusion

As technology continues to evolve, the importance of Faraday bags in law enforcement and military applications is likely to grow, ensuring that critical evidence and sensitive information remain protected. Incorporating Faraday bags into standard operating procedures is a smart move for any agency or unit looking to maintain the highest standards of evidence integrity and security.
Have any Questions or would like to place an order? We'd love to help! Chat with our friendly customer service team by calling 1-844-945-3625, chatting in on our website or email us at customersupport@wildoaktrail.com. We look forward to hearing from you!

Leave a comment
Comments will be approved before showing up.
